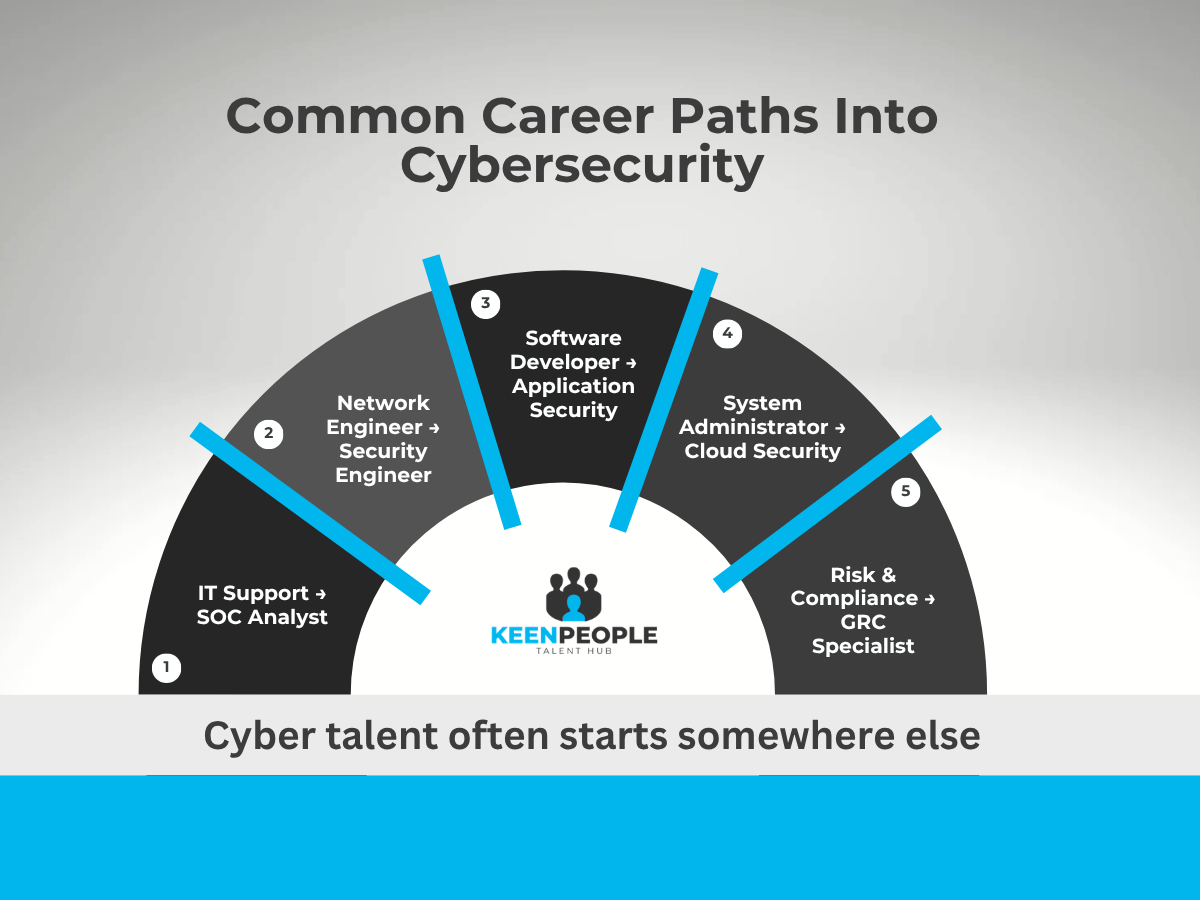
When people think about cybersecurity professionals, they often imagine someone who studied cyber from day one.
In reality, the path into cybersecurity is rarely that straightforward.
Many of today’s strongest cyber professionals started their careers in completely different areas of technology, and gradually moved into security as their interests and responsibilities evolved.
For hiring managers, understanding these career paths can open the door to a much wider talent pool.
Here are some of the most common routes we see.
• IT Support → Cybersecurity
Many cyber professionals start in technical support roles.
Working with infrastructure, systems, and troubleshooting gives them a strong foundation for understanding vulnerabilities and system behaviour.
Common transition roles include:
• Security analyst
• SOC analyst
• Vulnerability analyst
• Network Engineering → Security Engineering
Network engineers already understand how systems communicate and where weaknesses may appear.
This knowledge makes them particularly strong candidates for roles such as:
• Network security engineer
• Security architect
• Infrastructure security specialist
• Software Development → Application Security
Developers who move into security bring something incredibly valuable: the ability to build secure systems from the inside.
Common transitions include:
• Application security engineer
• Secure software developer
• DevSecOps specialist
• System Administration → Cloud Security
System administrators are often responsible for maintaining infrastructure and access controls.
As organisations move to cloud environments, many transition into:
• Cloud security engineer
• Identity and access management specialist
• Security operations roles
• Risk, Compliance, or Audit → Governance and Risk Roles
Cybersecurity is not only technical.
Professionals from governance, risk, and compliance backgrounds often move into roles such as:
• GRC specialist
• Cyber risk analyst
• Security governance manager
Why This Matters for Hiring Managers
The cybersecurity talent pool is broader than it may first appear.
Many strong candidates bring valuable experience from adjacent fields.
Looking beyond traditional job titles can often reveal professionals who already have the skills, mindset, and technical foundation needed to succeed in security roles.